A friend of mine recently moved from EU to US and tried to log into his Amazon account. What happened afterwards could only be described as a comedy of errors on their behalf.
The first time he tried to log in, he got locked out of his account. That’s nothing new: IT companies have long refused to accept the existence of jet liners and overseas travel and most will respond with mild brain aneurysm if a customer frequently changes their physical or billing address.
It might seem like a trivial issue – all we need to do at this point is contact Amazon and ask to restore access. Well, not so fast…
Mistake #1 – Can’t talk to support unless logged in
Amazon usually has great customer support. I’ve personally dealt with them on numerous occasions and had nothing but great experience. The only problem here is – in order to contact them, one needs to be logged in:
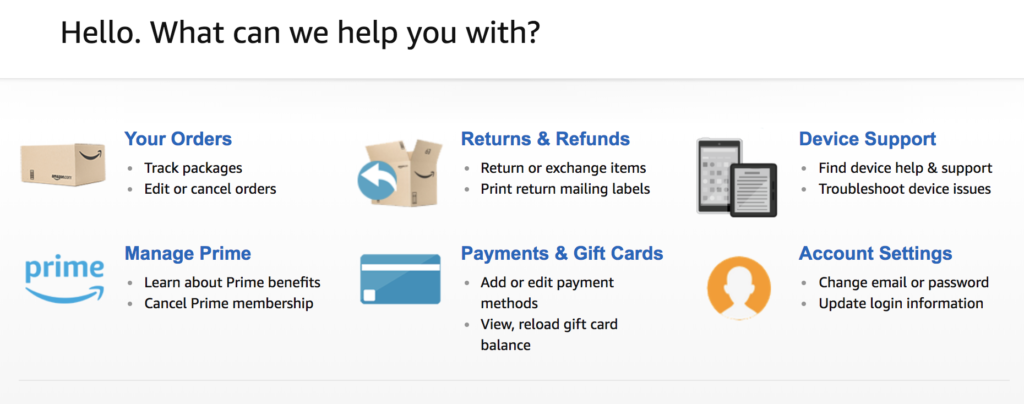
That’s not very helpful if you cannot access your account.
Perhaps calling their helpline would help?
Mistake #2 – No official phone number listed
Since all options under “help” are pretty useless, let’s try “Need More Help?” and then “Contact Us”:
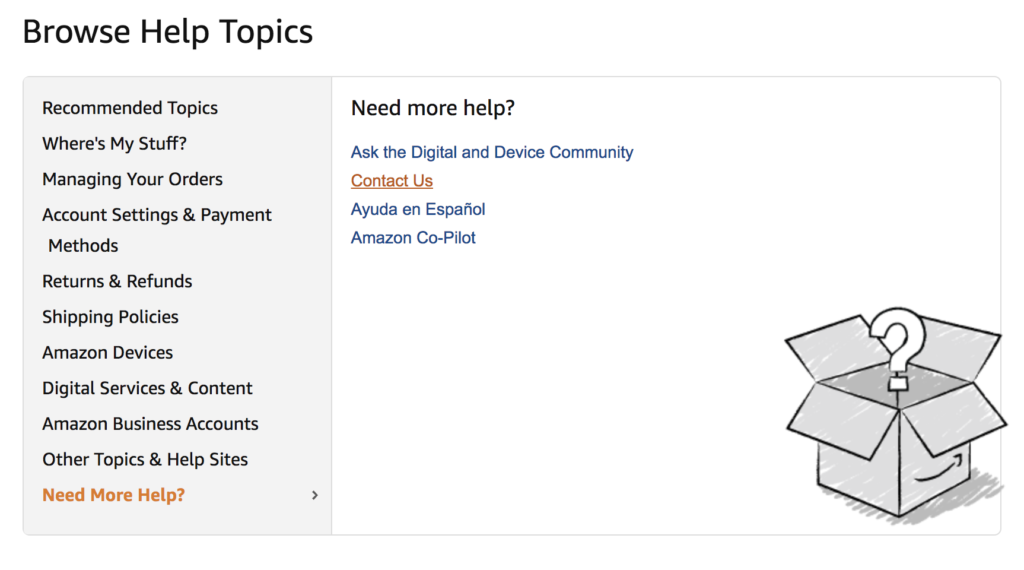
Surely they must list their phone number somewhere on the website? Here’s Amazon’s footer:
Just look at all these helpful links! Film Festival submissions, online shopping in India, even “Deals and Shenanigans”. No phone number, though.
So what my friend did was he googled a phrase like “amazon account phone number” and got one of these wonderful websites in response:
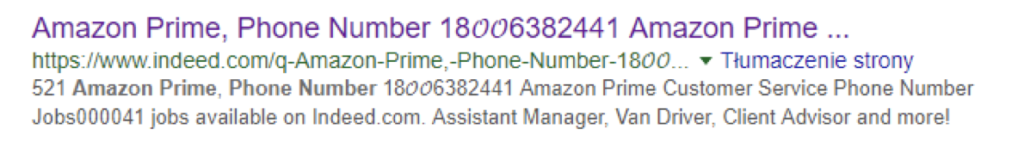
From that point, it was a downhill ride. After he got in touch with “security department of Amazon” (wish I could do an accent here), they asked for his login email and offered instant help. In the email that arrived 2 minutes later, they suggested to log into his computer, set up a new “secure paypal” account and perform a “bitcoin identity verification”.
It’s an online scam like any other – this particular group used XCoins.com to steel and launder money in one go as “personal loans”. What’s interesting, though, is the email the fraudsters sent.
Mistake #3 – SPF configuration of amazon.com
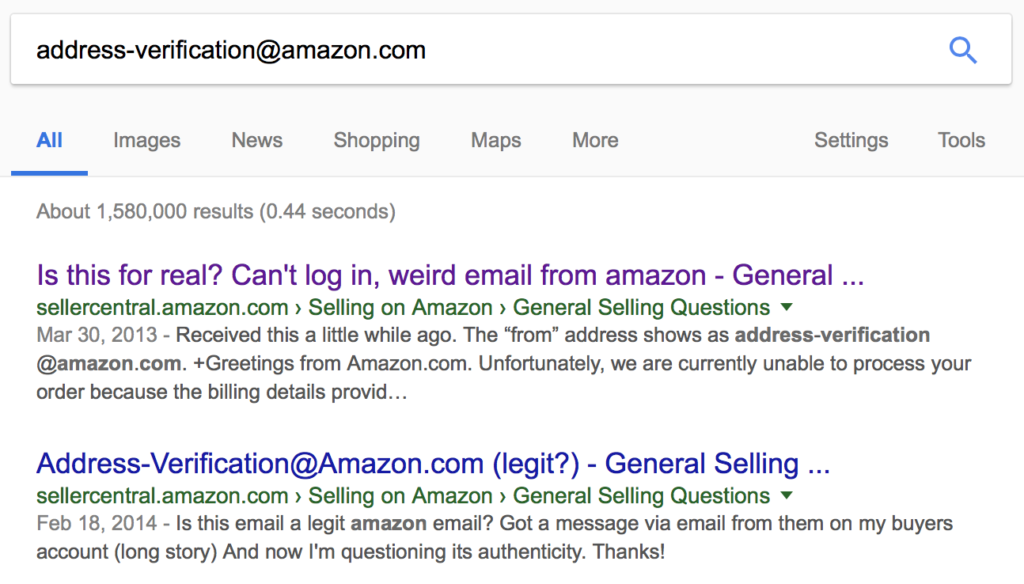
The email was sent from [email protected] – a legit address used by Amazon. In the email, they’re asking for billing information, address, the usual stuff – but it looks somewhat shady. So shady, in fact, that people had doubts as to its authenticity for years now:
In our case, the email had a bonus link, which allowed the fraudsters to install a remote support plugin and take over computer’s controls.
But in the era of SPF, DMARCs and DomainKeys, how can one spoof an email from amazon.com? Let’s look at their SPF records:
➜ ~ host -t TXT amazon.com amazon.com descriptive text "v=spf1 include:spf1.amazon.com include:spf2.amazon.com include:amazonses.com -all"
Whoa.
Amazon includes SES – their publicly available Simple Email Service – in their SPFs. In other words – they themselves provided our fraudsters with the infrastructure needed to scam people.
How To Fix It?
Easy. First, only corporate and non-public email relays should be allowed to send emails from amazon.com.
Second, provide a working phone number on your website. In the aftermath of this mess we finally called Amazon through my account and mentioned the other rogue number to them. Their response was mind boggling: “It’s a fake number, don’t use it”. Corporate responsibility at its best.
Finally, this whole situation is yet another example of extreme overkill security measures acting against end user’s best interest. Similarly to complex password policies, which effectively increase the chances of getting hacked (post-its anyone?).
Perhaps it’s just a method to save some money by reducing the staff of their call center. Whatever it is, if not for Amazon’s brick-wall policies, my friend wouldn’t have to cancel his credit card.