Microsoft’s own RDP client does not like their 1.3.6.1.4.1.311.54.1.2 key usage, contrary to MS own guidelines.
When connecting to RDP servers using Microsoft’s client for macOS, I encountered this weird situation:
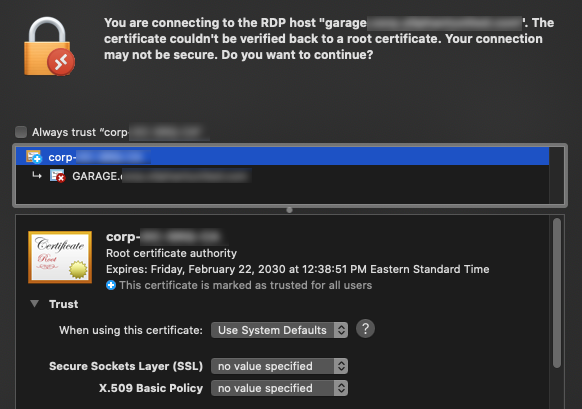
It looks like even though the certificate is issued by a trusted authority (corp), it’s still being rejected. Having investigated for 2 hours, I noticed that the RDP app cannot properly decipher “1.3.6.1.4.1.311.54.1.2“, which is the key usage code for “Remote Desktop Authentication“:
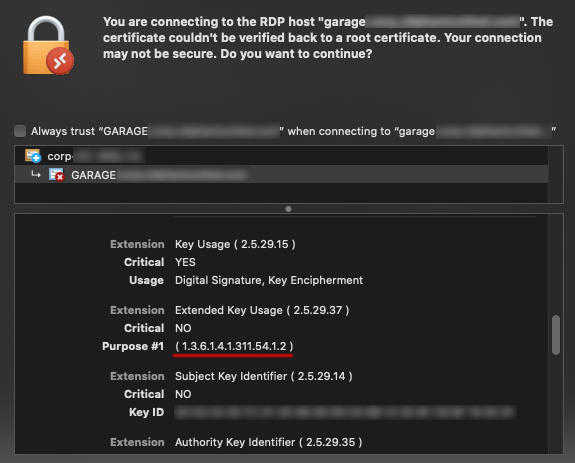
Microsoft references the same ID in their MSDN documentation. But taking into consideration it is Microsoft after all, I took the digital representation of their usage code as a sign that their own app has no clue what it’s supposed to mean.
Back at the CA, I added “Server Authentication” and “Client Authentication” to the template’s intended usage (I kept Remote Desktop Authentication just in case):
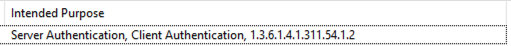
For this to have any effect, one needs to:
- Revoke the certificate at the CA
- Manually delete the certificate from the RDP server (under Personal certificates)
- Reboot the RDP server, since its keeps the old cert cached in memory
And just like that, the issue is no more. It would be really nice if Microsoft’s software followed their own guidelines.